One of the things we are quite proud of here at CSI despite the numerous network down stories over the years (many of them gruesome) we have never had a client miss a payroll. A business official’s worst nightmare is not that the network is down. It is that they might miss payroll.

Weekly Tech Tidbit – Disasters Happen. How Are You Going To Make Payroll?
Weekly Tech Tidbit – Vendor Support Contracts
This one is short and sweet. Once in a while we encounter equipment or software that you have purchased elsewhere, but you want CSI to actively support you with it moving forward. The reality with some of these vendors is that we are not allowed to call for technical assistance or even to place a […]

Weekly Tech Tidbit – 4 Hour On-Site?
Often we all don’t get true clarity on the importance of certain issues until you are living them. That is why for instance Dutchess County BOCES attempts to do a yearly, live, full DR test. It is amazing what you find out when you actually force yourself to go production on plan B. Documentation is […]

Weekly Tech Tidbit – Secure your DNS
Keeping up with my theme on DNS related posts, this week I will again reprise a post from over a year ago on the importance of implementing proper control of DNS as part of your malware protection program. It remains as valuable part of your overall all network and security management policies.
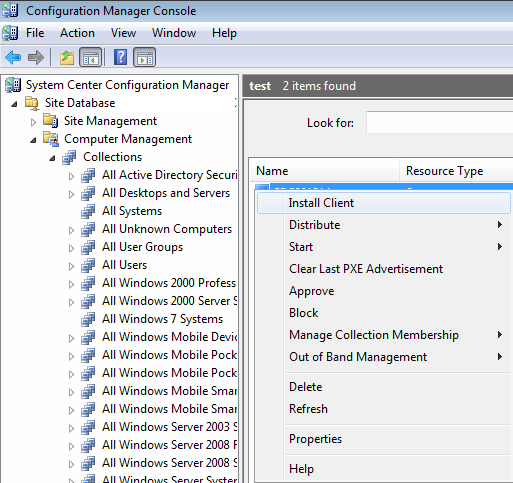
CSI Tech Talk Webinar – Troubleshooting SCCM Configuration Manager Part II – Introducing Support Center – Recording Available
In the February Tech Talk Webinar entitled, “SCCM Troubleshooting Part II” Scott introduced the new Support Center for client troubleshooting which became available in 1810. It provides real-time log viewing, or capturing the state of a Configuration Manager client computer for later analysis.
CSI Tech Talk Webinar – China Hacking Update – Recording Availabile
The US-CERT (Computer Emergency Response Team) recently gave a presentation on what China has been doing to hack anything they can hack with the goal of stealing intellectual property, money and personally identifiable information. While most public sector schools and government agencies are generally not vast repositories of intellectual property, they do manage and transfer […]

Weekly Tech Tidbit – It Happened Again. The Dark Side of Third Party Vendor Equipment On Your Network
We constantly harp on all of you segregating third-party vendor equipment on to vendor VLANs. The purpose of that is to keep third-party vendor equipment completely away from your internal network. Ideally, we don’t want these vendors to see, touch, or ask your internal network anything.
