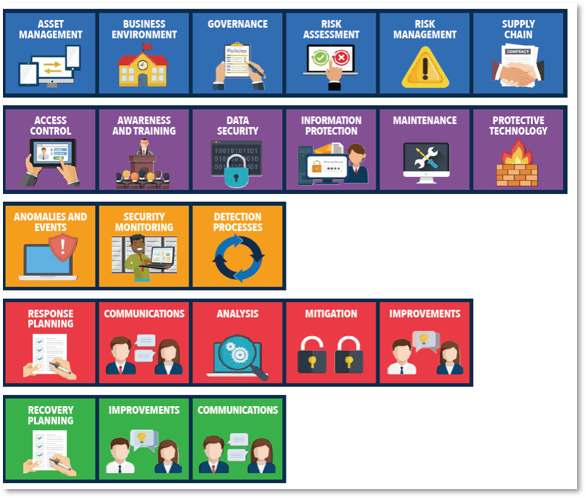
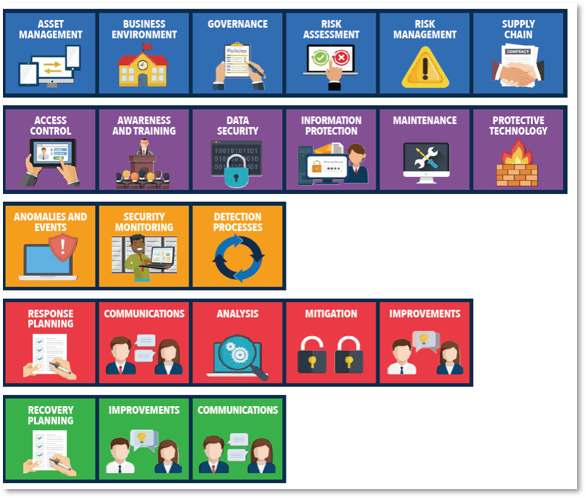
 As mentioned in last week’s Tech Tidbit, we have begun a new series of weekly bulletins sent to School Business Officials giving them more information on the changing Cybersecurity landscape and how the NIST Cybersecurity Framework can help them increase their security while complying with the Ed Law 2-d guidelines. So I decided that we would run some companion Tech Tidbits that will remind you of some of the many aspects of the complex NIST Cybersecurity Framework. As mentioned in last week’s Tech Tidbit, we have begun a new series of weekly bulletins sent to School Business Officials giving them more information on the changing Cybersecurity landscape and how the NIST Cybersecurity Framework can help them increase their security while complying with the Ed Law 2-d guidelines. So I decided that we would run some companion Tech Tidbits that will remind you of some of the many aspects of the complex NIST Cybersecurity Framework.
Today, I am going to take a moment to discuss inventory and control of software assets in the IDENTIFY category.
There are a number of practical ways to better control our software inventory.
If you are a Google Apps/Chromebook district, leveraging the Google Apps Admin console is a good way to keep tight controls on Chrome Extensions and other apps. Google has been on a mission to rid its platform of malicious or deceiving apps. You should do the same. Your users shouldn't be able to install anything you haven't approved.
In the Windows world, it has always been more of the wild west. To maintain control we need to start with the basics:
- Only have limited users
- Block Add/Remove Programs
- Implement our old-school "blacklists" and "whitelists" via Group Policy to keep your users doing what you want them to do.
- Implement software hashes and application certificates via Microsoft AppLocker to further lockdown software to only what you want.
- Implement a third-party application patching tool to patch your major applications to your vendor's recommended levels.
- Set up Compliance Management reports in Microsoft Endpoint Configuration Manager (aka SCCM).
- Deploy approved applications with an approved self-service tool found in many of the client endpoint management systems.
- Deploy Software Metering in Microsoft Endpoint Configuration Manager.
Ensuring software is supported goes beyond patch levels. It is a very precarious place to be when you are running End of Support/End of Life products in a production environment.
Most notable examples are:
- VMware ESX hosts
- Microsoft Windows OS
We have seen time and time again the district's neglect to keep current on foundational items "because it just works". Then something bad happens and the vendor won't assist in the recovery or charges exorbitant rates.
If you need help implementing any of these recommendations, please let us know.
-Scott Quimby |
You must be logged in to post a comment.