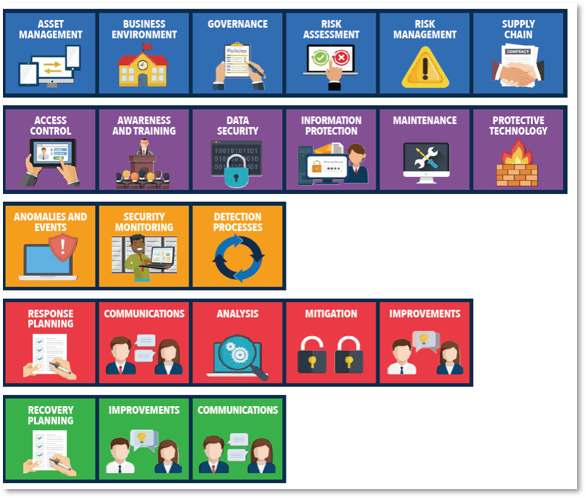
 This week I’d like to talk a little bit about the NIST Category - Recover. According to NIST, the Recover Category “identifies appropriate activities to maintain plans for resilience and to restore any capabilities or services that were impaired due to a cybersecurity incident. The Recover Function supports timely recovery to normal operations to reduce the impact from a cybersecurity incident.” That is a lot to unpack, so this week I am going to focus on one aspect of meeting that requirement - maintaining good backups. This is something we have all been doing forever, but as with many repetitive tasks, there can be areas that get missed. Because this is such a vital aspect of recovering from a cyber incident I wanted to share a few reminders. This week I’d like to talk a little bit about the NIST Category - Recover. According to NIST, the Recover Category “identifies appropriate activities to maintain plans for resilience and to restore any capabilities or services that were impaired due to a cybersecurity incident. The Recover Function supports timely recovery to normal operations to reduce the impact from a cybersecurity incident.” That is a lot to unpack, so this week I am going to focus on one aspect of meeting that requirement - maintaining good backups. This is something we have all been doing forever, but as with many repetitive tasks, there can be areas that get missed. Because this is such a vital aspect of recovering from a cyber incident I wanted to share a few reminders.
- Read your daily backup logs. It doesn't help you if your backups are failing each night and no one is fixing that. Please make it someone's specific daily responsibility to do this.
- Routinely test your backups. You must prove that they work. There are two levels to this. The first is spot checks of file restores to prove you can retrieve your data. The second level is to actually attempt to recover a server. This can be done in a sandbox so you don't disrupt normal day-to-day activities. A full test recovery requires time and focus.
- Make sure your backups are encrypted and password protected. This is especially true on cloud backups as the Cyber insurance companies have been really focused on this area.
- If you have multi-factor authentication options to get to the backup management console, please fully implement them.
- Make sure you have a regular process that creates air-gapped backups so that even if your systems are compromised, there is a good backup somewhere physically separate and disconnected that cannot be accessed in any way from the main system.
If you need help sorting any of this out, please give us a call.
-Scott |
You must be logged in to post a comment.