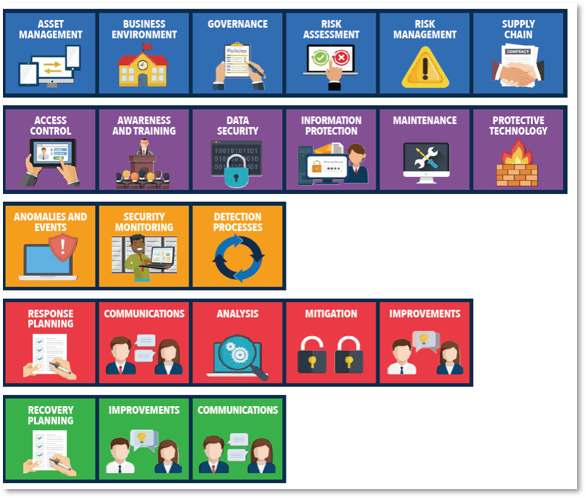
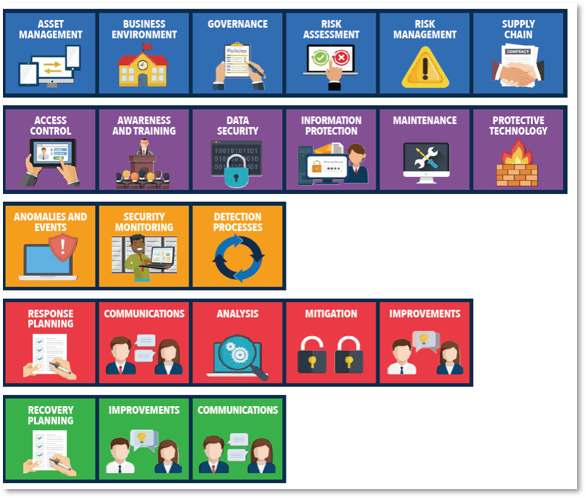
 This week I would like to talk to you about Malware Defenses. This topic is in the NIST Detect and Protect categories. This week I would like to talk to you about Malware Defenses. This topic is in the NIST Detect and Protect categories.
Antivirus has been around for what seems like forever. However, as long as antivirus has existed, we have had the problem with getting it on "all" servers and "all" endpoints. Most people do a pretty good job of getting some sort of antivirus on most devices. Unfortunately, that is like saying “Well, I locked most of my doors and windows” and then be surprised if someone breaks into your house. All that is needed is ONE way in.
As I do work on various servers, I find servers without any sort of basic protection or endpoints that have protection issues.
Endpoint protection is vital. You must make sure you have at least basic antivirus protection on all your Windows, Linux, and Macintosh devices on your network, and make sure it stays current.
Most commercial antivirus products have a central console to gauge the status of your endpoints. Use that console to stay up-to-date on the status of antivirus on your devices.
Microsoft Windows Defender doesn't have a central console per se. However, Microsoft Endpoint Configuration Manager (aka SCCM), Huntress, and some other third-party products provide a centralized console.
Once you know that your AV solution is installed and current, you should protect removable devices. USB device control is a whole topic unto itself. Then the next step is to prevent content from auto-launching.
The stressor for most people is scheduled scans for endpoints. You should be doing scheduled scans regularly so that newer signatures can re-evaluate your files again to prevent something bad from getting past your first-line defenses and staying hidden. Server scans are generally not hard to schedule, but workstations must be on and we understand you have to balance performance issues against end-user functionality. It can be hard to do, but it must be done.
This article is only covering basic solutions for basic issues. There are also much more sophisticated, robust endpoint defenses that exist, but it is important to get basic security in place before moving on to the more complex
If you'd like to discuss how to get a handle on your endpoint protection strategy or are ready to discuss more complex solutions, give us a call.
-Scott Quimby |
You must be logged in to post a comment.