Ransomware and Incident Response: How Security Controls Help Districts Reduce Risk and Prepare for Action (and achieve Ed Law 2-d Compliance) – Recording Available
Speaker: Alan Winchester, Chief Development Officer, Caetra.io
Alan Winchester is the Chief Development Officer and creator of CyMetric™. His vision is to enable customers overwhelmed with the issues surrounding legal compliance to meet their obligations intuitively and simply, reducing the need to incur the expenses of consultants and lawyers. Alan leverages his years of experience as a cybersecurity lawyer for the benefit of Caetra.io and its customers.
Ransomware and Incident Response: How Security Controls Help Districts Reduce Risk and Prepare for Action (and achieve Ed Law 2-d Compliance)
Session Description:
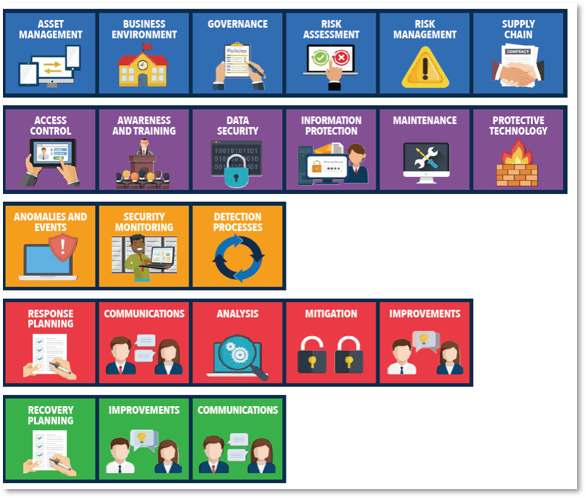
Global cyber incidents in the education space are skyrocketing and educational institutions are struggling. To reduce their risk, Districts are seeking to develop incident response plans that: align with their cybersecurity programs; prioritize systems and data sets; understand the process to secure (and limitations of) cyber-insurance policies, and effectively manage incidents as they occur. This effort is especially tested in the area of ransomware. Developing an understanding of how the security controls required by the NIST CSF can address these challenges and how their implementation helps districts protect their data will better equip them to respond to incidents of this kind. In this program, we will discuss what security controls mean to educational institutions and how those institutions can identify gaps in their critical risk areas and how to close them. Topics will include NIST CSF subcategories and controls, vendor and contract review, transactional due diligence, evaluating cyber insurance policies, and counseling staff and board members on the scope of the risk and need for affirmative action. Attendees will gain an understanding of how to define and assess their current cybersecurity programs and protocols, define policies and controls that meet not only the legal requirements of various laws but also recommends the required NIST-based technical functions and procedures needed to protect information assets, monitors changes to NYS cyber requirements, and identify high-risk scenarios for prioritization along with emergency response plans to mitigate those scenarios.
To watch this recording click here.
