 In last week’s email, we talked about the first NIST Cybersecurity Framework category – Identify. This week we will be discussing the second category – Protect.
In last week’s email, we talked about the first NIST Cybersecurity Framework category – Identify. This week we will be discussing the second category – Protect.
The idea of protecting yourself and your network is pretty straightforward general concept. But what specifically do you need to do? Let’s see what NIST tells us - according to NIST, the Protect Category outlines appropriate safeguards to ensure the delivery of critical infrastructure services. The Protect Function supports the ability to limit or contain the impact of a potential cybersecurity event.
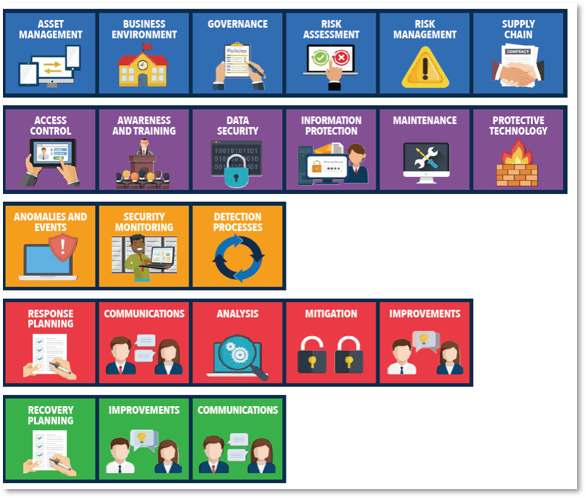
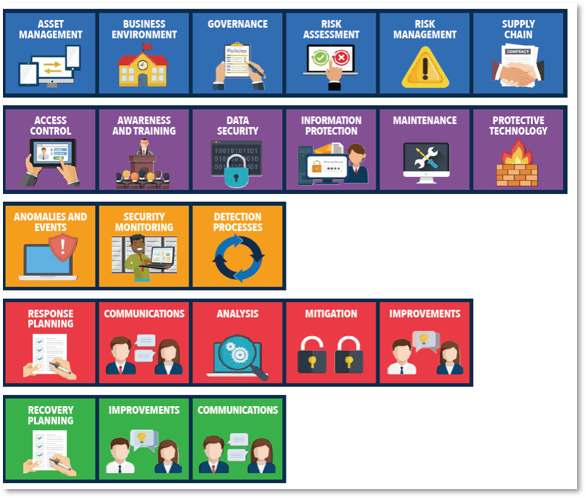
Here are the specifics according to NIST:
Identity Management, Authentication, and Access Control (PR.AC): Access to physical and logical assets and associated facilities is limited to authorized users, processes, and devices, and is managed consistent with the assessed risk of unauthorized access to authorized activities and transactions.
Awareness and Training (PR.AT): The organization’s personnel and partners are provided cybersecurity awareness education and are adequately trained to perform their information security-related duties and responsibilities consistent with related policies, procedures, and agreements.
Data Security (PR.DS): Information and records (data) are managed consistent with the organization’s risk strategy to protect the confidentiality, integrity, and availability of information.
Information Protection Processes and Procedures (PR.IP): Security policies (that address purpose, scope, roles, responsibilities, management commitment, and coordination among organizational entities), processes, and procedures are maintained and used to manage the protection of information systems and assets.
Protective Technology (PT.PT): Technical security solutions are managed to ensure the security and resilience of systems and assets, consistent with related policies, procedures, and agreements.
Here are some examples from NIST:
- Protections for Identity Management and Access Control within the organization including physical and remote access
- Empowering staff within the organization through Awareness and Training including role-based and privileged user training
- Establishing Data Security protection consistent with the organization’s risk strategy to protect the confidentiality, integrity, and availability of information
- Implementing Information Protection Processes and Procedures to maintain and manage the protection of information systems and assets
- Protecting organizational resources through Maintenance, including remote maintenance, activities
- Managing Protective Technology to ensure the security and resilience of systems and assets are consistent with organizational policies, procedures, and agreements
As with the Identify category, you can see there are many aspects to protecting your network and data. And just like the Identify category, the important thing is to start. Take a look at our suggestions below. If you would like even more help in navigating the NIST Cybersecurity Framework give us a call.
Next week’s email will discuss category 3 – DETECT.
This week’s suggestion:
- Talk to your Director of IT about how many people have access to an administrator id. We generally recommend limiting the number to 3-4 people. Also ask if they have their own personal administrator-level id, or if multiple people are sharing the administrator id. We recommend having personal administrator ids so you can track and control access.
- Ask your Director of IT about the use of multi-factor authentication (MFA) for sensitive data and applications. This function can continue to protect you if a userid and password have been compromised.
If you and your Director of IT would like to schedule a time for a more in-depth discussion with one of CSI’s knowledgeable engineers, or if you simply would like more information, please contact Lisa MacDougall at lmacdougall@csiny.com or call 845.897.9480.
You must be logged in to post a comment.