As you present a better and better network defense, the bad guys continue to get more creative in their attacks. A new attack that has shot out of nowhere to instantly become very prevalent is the “Fake Captcha” attack. It is about two months old. Our partner SOCs report this as the new scam in […]
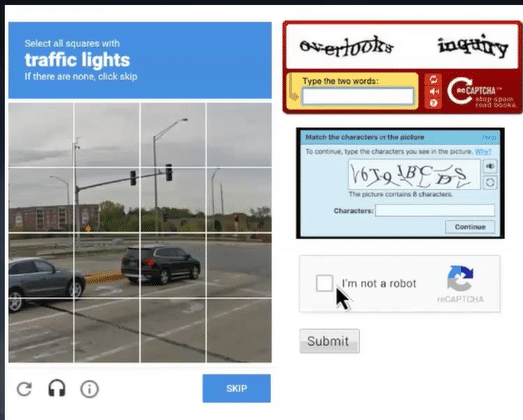
Tech Tidbit – Warning Fake Captcha Attacks Are Delivering Malware

Tech Tidbit – The best defense may be a good offense
“The best offense is a good defense.” -Author Unknown “The best defense is to go on offense.” -Scott Quimby If you have been reading our Tech Tidbits over time, you know that a Security Operations Centers (SOCs) that provide 24x7x365 “eyes on glass” over your endpoints, or better still, over your entire network and firewalls, […]
Acture/CSI’s January Tech Talk – Recording Available
This exciting session will be led by Scott Quimby, CISSP, Senior Technical Advisor at Acture/CSI, and Larry Lanigan, Site Leader at Acture with 17 years of experience as a technology professional. What to Expect: 1. “Tech Tidbits” with Scott Quimby.
Exclusive Cybersecurity Webinar with Acture/CSI and Blackpoint Cyber Experts – Recording Available
We are excited to invite you to an exclusive cybersecurity webinar recording led by industry experts at Blackpoint Cyber. This is your opportunity to gain insights from experts in cyber defense. Agenda: Introduction & Background of Blackpoint – Jamie Ivers, Senior Solutions Advisor SOC Overview – Jason Rathbun, Technical Director of Threat Operations SOC Saves: Real-World Examples – […]

SentinelOne MITRE ATT&CK Enterprise 2024 Results – Recording Available
MITRE is a not-for-profit organization that operates federally funded research and development centers (FFRDCs) to provide technical expertise and innovative solutions to various U.S. government agencies. MITRE focuses on national defense, aviation safety, cybersecurity, healthcare, and more.

Tech Tidbit – My training day security event
I am sitting at my desk doing what I love—training Acture/CSI’s next generation of engineers. I am teaching them about Active Directory theory and operations. I am demonstrating how the Active Directory Recycle Bin works. I created a test ID in AD – Steve McQueen.

Tech Tidbit – Flash Drill – How Would Your Team Handle This Superintendent Request?
Today is a flash drill exercise. The Superintendent just told you that a retiring employee went rogue on the last day of school and sent a defamatory email to the entire district email distribution list. The Superintendent and your district legal counsel are asking you these questions: Where did the email go? Did it leave […]

Tech Tidbit – A discussion about insider threats
Acture/CSI has been going at a dizzying pace. I counted 16 online and in-person events for 2024, plus NYSCATE. Then you add all the Acture Solutions events. The Acture Solutions family has been busy providing you with the best technical information and best products to support you in maintaining a stable, secure, manageable network for […]

Tech Tidbit – Spring Break. I need only two things from you!
I am sticking you with real work for Spring Break. My list is very short. I need you to update, patch, and scan your servers and endpoints I need you to recalibrate all your APC UPSes. Remember to do it only on a nice calm day without weather or wind.

Tech Tidbit – Flash Drill – How Would Your Team Handle This Total Blindside Event?
Today is a flash drill exercise. The warm weather has arrived. It is Thursday afternoon of Memorial Day weekend, and the district gave back an unused snow day, making it a four-day weekend. The weather forecast is ideal. Everyone is bugging out to enjoy themselves.
